When people are skilled, they make the things they are able to do look so easy. My son in law solves complex computer mysteries …
Aug 9, 2017 - When people are skilled, they make the things they are able to do look so easy. My son in law solves complex computer mysteries with a few clicks of his mouse. Olympic sprinters break speed reco…

Security Nation] Mike Hanley of GitHub on the Log4j Vulnera

Dandelions Dandelion, Dandelion designs, Book cover illustration

Xenomorph Malware Burrows into Google Play Users, No Facehug

2.10 Exercise.docx - AP CSP 2.10 Exercise Project Stem The first
These mystery reading passages allow your student to become a detective and solve mysteries! It targets reading comprehension, making inferences,

Solve Mysteries by Inferences and Predictions Reading Comprehension Passages

Log4Shell 2 Months Later: Security Strategies for the Intern

When people are skilled, they make the things they are able to do look so easy. My son in law solves complex computer mysteries …

Pin by Kantawat Shamshoi on ป้าย Borders and frames, Frame, Borders for paper

Samsung Confirms Lapsus$ Ransomware Hit, Source Code Leak
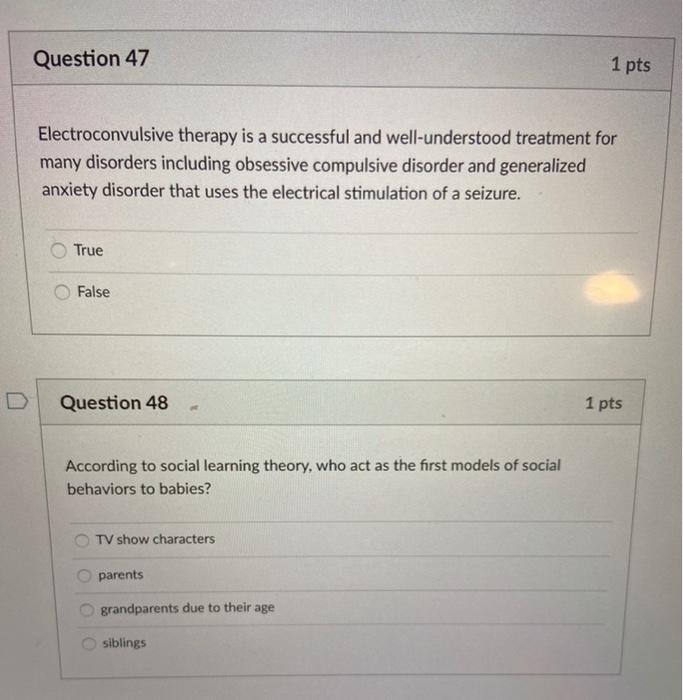
Solved Question 45 1 pts Insane and mentally ill have the

Educational Equity, Politics & Policy in Texas: October 2011

Mtra. Anita 🍎 adlı kullanıcının Dibujos Clips panosundaki Pin
Slang-Challenge/train.csv at master · josephenguehard/Slang
Data/newsDB.json at master · TextyML/Data · GitHub

Okta Says It Goofed in Handling the Lapsus$ Attack - vulnerability